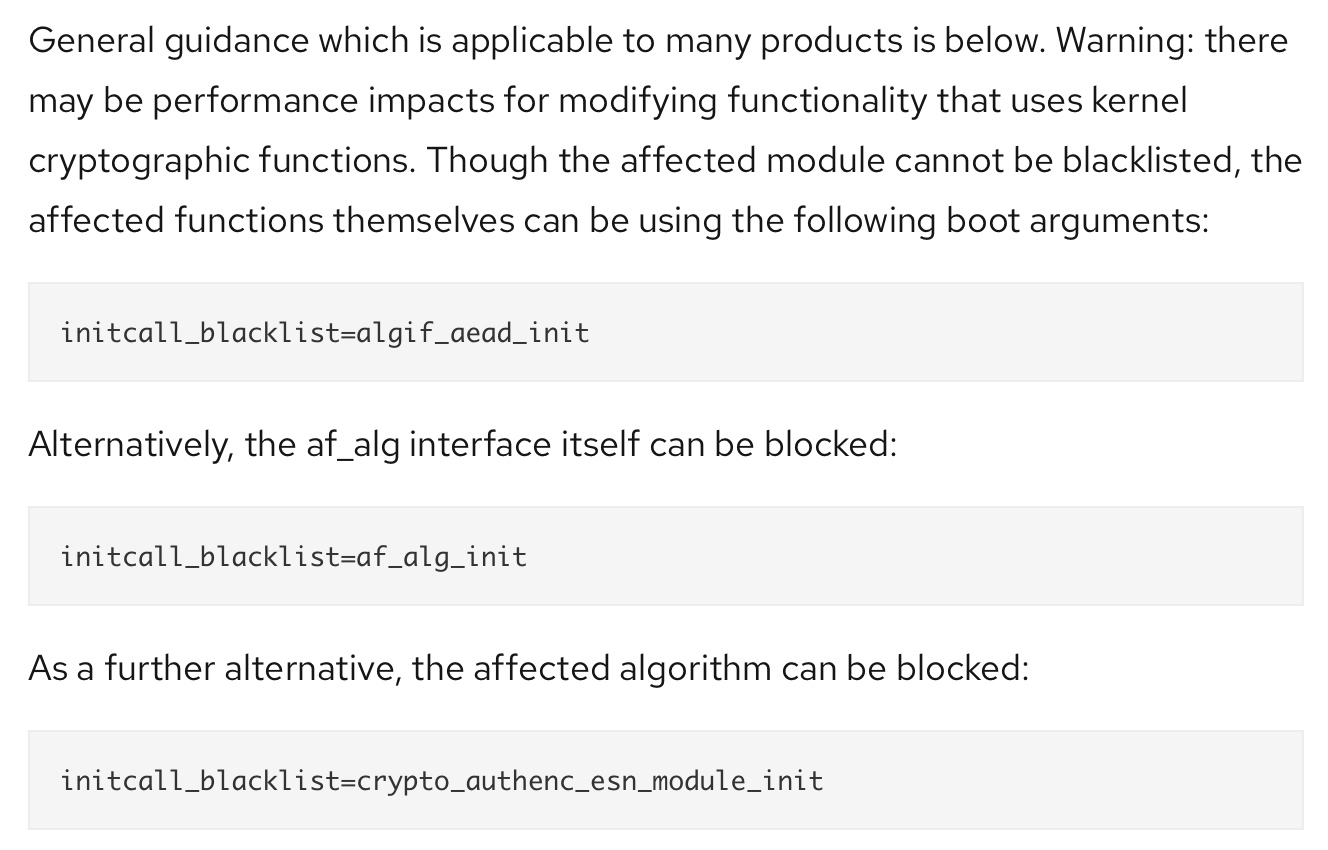
Ah, the #copyfail clickbait posts are coming. Here’s my serious contribution. On your Linux machine add
initcall_blacklist=algif_aead_init
to your kernel boot commandline (typically in grub). Reboot. You are now safe until the updated kernel packages become available. For distributions with the `grubby` command this is done as root with
# grubby --update-kernel=ALL --args="initcall_blacklist=algif_aead_init"
This mitigation comes courtesy of Red Hat. Our engineers keep you safe :)
1/4